Комментарии:

No le entiendo. :(
Ответить
Can you pin me
Ответить
G-R-E-A-T WORK THE PICTURES MAKE IT VERY UNDERSTANDABLE
Ответить
Impressive 🎉
Ответить
Thank you so much!
Ответить
Poorly made. Skipping lots of fundamental steps. Anyone saying this is a good video, try do it yourself using a piece of paper, using new P and Q primes, and the same steps.
Ответить
Amazing. Beautiful. Helpful. I could not have asked for a better video on the topic
Ответить
Please understand it . Explain slowly this sounds like garbage slowly explaining it will be good
Ответить
video cut
rapping faster than eminem
.. Uh, summa-lumma, dooma-lumma, you assumin' I'm a human
What I gotta do to get it through to you I'm superhuman?
Innovative and I'm made of rubber so that anything
You say is ricochetin' off of me, and it'll glue to you and
I'm devastating, more than ever demonstrating
How to give a motherfuckin' audience a feeling like it's levitating
Never fading, and I know the haters are forever waiting
For the day that they can say I fell off, they'll be celebrating

Thanks this was a high quality content and helped me a lot
Ответить
Well explained...
To make it interesting this is the public key or address mt3Au8iBxTUNcrkZ6ESTHJu8Vsd2VaE2Cv
there is a prize for the one who finds the secret key, (which is related to the video)
Don't go crazy, it has no economic value, it's just a challenge. ;)

something is not right here
Ответить
คนไทย???
Ответить
Show us the steps to get to e=35 help man
Ответить
What's the rush, it's not a race
Ответить
Less caffeine, please. The narration of the example was about 3X what it should have been.
Ответить
For the first time in my life I had to slow a video down
Ответить
Useless video
Ответить
very fast cant catchup
Ответить
too fast
Ответить
e must be prime with phi(n)
Ответить
Don't know if this helps but:
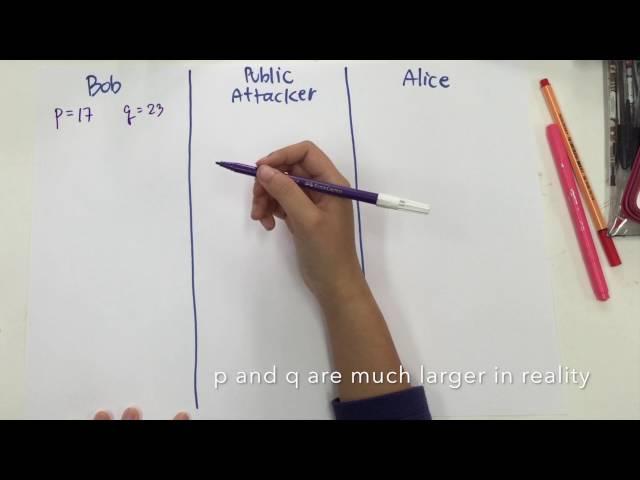
1. Choose 2 large prime numbers P and Q.
2. Calculate N = P x Q
3. Select the public key E such that it does not have a common factor as (P-1) x (Q-1).
4. Select the private key D such that: (D x E) mod (P-1) x (Q-1) = 1
5. For encryption, calculate the cipher text CT from the plaintext PT as follows: CT = PT^E mod N
6. Send CT as the cipher text to the reciever
7. For decryption, calculate the plaintext PT from the ciphertext CT as follows: PT = CT^D mod N

there are 3 people explaining in a 5 minutes video... great.
Ответить
Awesome video! I believe it is Fermat's Little theorem, unless there are alternative spellings for his name
Ответить
great video thanks
Ответить
whats this nonsense
Ответить
What the fuck?
Ответить
it's shamir not shimar..
Ответить
saved my exam
Ответить
If p =7 and q =11 how to find d??
Ответить
I just watched this for the lols I have no clue what this is saying
Ответить
N O I C E - it's clear and understandable!
Ответить
you lost me at your 3 lines equal sign....
Ответить
THANK-YOU.
Please to rap XD

e is introduced out of nowhere and is never explained.
Ответить
I have RSA deciphered from boredom :-)
mod(n, round(x))=0 gives immediately p and q

To the point
Ответить
9999999999999999999/10 !!!
Ответить
Thanks for the video - it really helped me to understand RSA encryption in a short period of time.
Ответить
Straight to the point. 11/10.
Ответить
why is the message in the example a number? Is the message usually in bytes, so its a number?
Ответить
Thanks for the vid, was great to learn from you
Ответить
Nice Video. Great Work. Keep It Up!
Ответить