Комментарии:
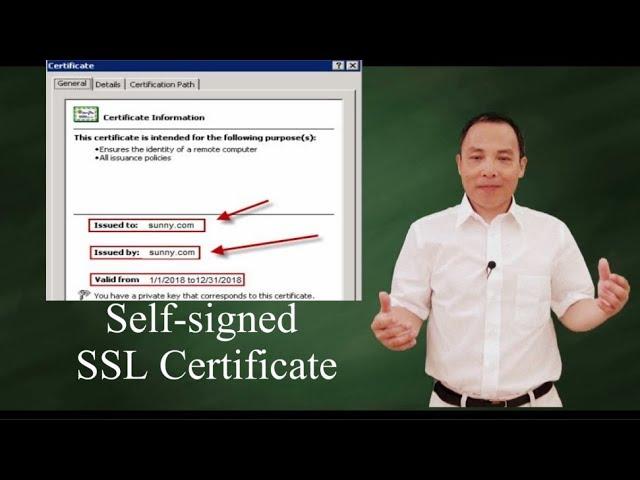
PKI: self-signed digital certificate?
Sunny Classroom
LAS LEYENDAS MÁS ATERRADORAS DEL NORTE DE MÉXICO
Relatos de la Noche
Olga Tañon - Me Subes Me Bajas Me Subes (Official CantoYo Video)
CantoYo Video Lyrics
Knowing Trailer 2
ChandlerCanterburyRS
Statistical Assistant |COMMERCE |SEBI & Stock Exchanges |KERALA PSC 2025
Emfavour LEARNING APP
Ananas OHNE verklebte Finger AUFSCHNEIDEN
SelberMachen
Чёрный Ворон - песня
Nico777t