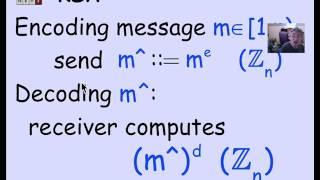
2.4.1 RSA Public Key Encryption: Video
Комментарии:

If the sender uses RSS algorithm. So he gets two keys Public and Private. If I want to send someone to public key . By What Method . How will I reach that public key.
Ответить
Well explained...
To make it interesting this is the public key or direction mt3au8ibxtunkz6esthju8vsd2vae2cv
There is a prize for whoever finds the secret key, (which is related to the video)
Do not be crazy, it has no economic value, it is only a challenge.

Modern high performance RSA decryption does not use d and mod-N arithmetic (m = c^d mod N). It uses dp = d mod (p-1), dq = d mod (q-1) and qInv = q^-1 mod p.
This enables calculating m = c^d mod N much much more efficiently with half the number of bits (log(N)/2 bits) numbers as follows -
m = m2 + h q where m1 = c^dp mod p, m2 = c^dq mod q and h = qInv x (m1 - m2) mod p.

didn't NSA leave a backdoor in RSA? that is note since 2008. i think RSA as a company was liquidated soon after.
i believe some other method is being used based on some curve

Should give more examples
Ответить
thumbnail in the sky... outstanding destiny
Ответить
e is most commonly chosen to be a small prime number, rather than rel. prime to (p-1)*(q-1)
Ответить
But how can the sender be sure that the sender's public key actually has been created by that receiver and not some spy? :q
The spy can easily generate his own pair of keys, and then pretend to the sender that this is the receiver's key.
When the sender encrypts his message with it, the spy will be able to decrypt it easily, then encrypt again with the receiver's key and send it to him so that he didn't notice any tampering :q
How can we protect against that?

Go to a primary school and try again - there. Then re-record.
Ответить
I will decompose the RSA of any complexity into multipliers. Fast and not expensive.
Ответить
Awesome!!!
Ответить
My mind exploded.
Ответить
thanks..I like the explanation very much
Ответить
Thank you for this video.
Ответить