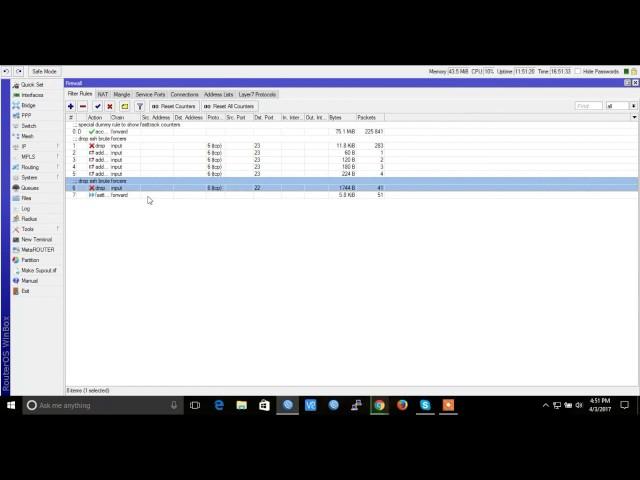
Mikrotik 100% CPU Usage and High CPU Usage Problems Solved
Комментарии:

tnx vai
Ответить
Thank you!
Ответить
Bang ijin tanya, mikrotik saya load cpu sampe 75% tinggi banget gara2 ramnya kecil atau storage kecil, atau apa ya bang, di tunggu responnya.
... mikrotik saya ramnya 256mb storage 128 mb

Спасибо помогли решить проблему, из за этого пропускная способность на бридже была 30-50 максимум, как только включил это правило, полетело под 200
Ответить
Manoooooo como assim ??? Muito obrigado cara eu te amo
Ответить
why do you have to masquerade the network
Ответить
Sorprendido!! Me Resulto Tu Video... Me Suscribo!
Ответить
Thank You
Ответить
Thank you. You saved my day. You king
Ответить
LOL
Ответить
Ggkgkgk... i got LOL
Ответить
con su huevada de gring0 solo genera perdida de paquetes, gring0 idiot4 es como su f35 q ni vuela
Ответить
By the way, this video SUCKS. You haven't got a goddamn clue what you're talking about, you're disabling the security features of the router, and you're bypassing all sorts of useful features.. Sure your CPU load is going down.. You've turned the router into a fucking switch..
Ответить
are you fucking serious? Christmas music on a goddamn video? Yeah, that'll be appropriate for 11 months of the year...
Ответить
Vc não vai poder mais colocar limite de banda vai liberar tudo para todos 😏
Ответить
Qos and firewall not working with fasttrack. Better buy hap ac2 or rb4011 or ccr for higher performance
Ответить
This will make all your queue disable.. Other words bypassing your limit queue..
Ответить
What a horrible advise. This is how you get PWNED!
Ответить
aqui liberou a internet de todos os clientes
Ответить
Parabéns pela dica resolveu meu problema numa simples aula na pratica show!!
Ответить
Thank u so much
Ответить
bagus..tpi simple queues trafiknya kog kecil ya?
masalah apanya y bos

gracia por la ayuda
Ответить
you'd by pass the qos by using the fast track...
Ответить
thanks
Ответить
Update your Firmware of your Mikrotik. There was a vulnerability in that version
2CVE-2017-83383992017-05-182017-06-01
7.8
NoneRemoteLowNot requiredNoneNoneCompleteA vulnerability in MikroTik Version 6.38.5 could allow an unauthenticated remote attacker to exhaust all available CPU via a flood of UDP packets on port 500 (used for L2TP over IPsec), preventing the affected router from accepting new connections; all devices will be disconnected from the router and all logs removed automatically.3CVE-2017-72854002017-03-292017-04-10
7.8
NoneRemoteLowNot requiredNoneNoneCompleteA vulnerability in the network stack of MikroTik Version 6.38.5 released 2017-03-09 could allow an unauthenticated remote attacker to exhaust all available CPU via a flood of TCP RST packets, preventing the affected router from accepting new TCP connections.

Thanksss
Ответить
EXCELENT!!!! THANKS VERY MUCH MATE
Ответить
not working speed slow down
Ответить
Thanks A Lot brooooo :D
Ответить
thanx 4 u
Ответить





![[WORDPRESS] Error Fixed / Download Backup File of All in one wp migration tool [WORDPRESS] Error Fixed / Download Backup File of All in one wp migration tool](https://invideo.cc/img/upload/a3FFZHFSSUUzUU4.jpg)


















