Комментарии:

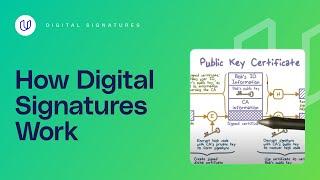
This is very well explained. I've had problem with one thing only, I didn't hear explicitly mentioned that CA send the signed hash of the message ALONG WITH the message (unhashed, unsigned) itself, so Alice receives the 4 part middle block in video, she calculates hash of message and decrypts signature, than compares hashes of the two.
Ответить
What would happen if the data sent to B were all encrypted together?
Ответить
What I found confusing, is when you say CA private key and CA public key, do you mean those are Bob's key? What are CA keys?
Ответить
Terrible video from start to begining. Talking really fast, only brief explanations, "and so on" is never a good sentence in any lesson, the image is bloated and not accurate. Plus you're hard to listen to. Crap, except for the shallow explanation of the original problem.
Ответить
great video, thanks!
Ответить
Is the certificate encrypted by CA or is it clear text and just the CA signature that is encrypted?
Ответить
The user must compare hashes in the end, but how does the end user know what kind of hash to perform on the original unsigned certificate so that it will match the original hash? Is this information also stored in the unsigned certificate?
Ответить
Simply excellent. In a short 3 mins video, explain digital certificate to its core and better than any other much longer videos out there.
Ответить
thanks, short and clear 👍
Ответить
is there any pythonproject for this explanation ?
Ответить
public key can be used to decrypt data encrypted by private key and vice versa.
Ответить
A part of the diagram that I found confusing was the attachment of the 'Signed certificate' rectangle at the bottom of the ID, Bob's public key, CA information. An improvement would be to include a separation between the CA information block and the Signed certificate block.
Ответить
Easy to understand, great video!
Ответить
You missed saying that the Bob's ID and all that was attached to the encrypted message (Alice cannot just """extract""" that info) , that is how Alice can create the hash to the orig messages unsigned. Otherwise you refer to the hash messages obtained by decryption twice!
Ответить
but how the recepient will verify the signature ??
Ответить
thanks for the diagram, it was good
Ответить
But to decrypt message attackers need bob's private key(asymmetric type), so they can't extract data right?
Ответить
Thanks, i was always confused about how the certifiacte is verified, but you make this very clear (with the public key by the CA decrypting the signature and then comparing the so revealed hash with the hash you generate from the payload of the certifiacte).
Ответить
This is an excellent explanation on how a browser validates authenticity of a certificate. A must see video. I could not find better explanation anywhere else.
Ответить
Finally... a perfect, on-point, explanation for how CA certs are used to validate the source's public asymmetric key. Namely, comparing a decrypted "signature" (hash) using the CA's public key with a hash of the remaining certificate components. Excellent. Thanks.
Ответить
hiddentoolz on lg.. best ever on prvt keys, thanks to those who recommended them❤️😝
Ответить
Thank you for your great explanation.
Ответить
perfect
Ответить
Short and clear note
Ответить
Pog Champ dude
Ответить
The kingz_0689 on ig he’s the best giving keys 🔑🇱🇷🔑🔑
Ответить
Nice explanation, got some points though for accuracy:
1- The video needs to be renamed to something that is more relevant to public key certificates
2- CA's private key is COMBINED with the hash code to generate the digital signature, it is NOT used to encrypt the hash code
3- CA's public key is used to EXTRACT the message digest (hash code), it is NOT used to decrypt the digital signature

Can I have a question? In all docs I have read the private key is only for decrypting but your demo shows encrypting private key for signature. So what is true ? :-)
Ответить
This is great explanation, clear, accurate!
Ответить
Change the title to Digital Certificates
Ответить
a little to fast, but still very good!!!
Ответить
engineer what do you thing of proof of signature protocol in XBY xtrabytes blockchain ecosystem?????
Ответить
Thanks for the video. One naive question. How Alice would extract the Bob's Id, Public Key and CA information from a signed certificate?
Ответить
The Title is a little bit misleading but through the thumbnail i understood that the content of the video was exactly what i was searching for, sir please change the title to something like How Digital Signatures are used with Digital Certificates, this will help many people as your video really explains the key concepts of this, thank you very good job!
Ответить
I can not understand someone speaking English, but their diagram is enough to understand the process. Congratulations! Thank you!
Ответить
Thanks for the video, You explained clearly in 3 minutes
Ответить
Good and clear explanation with 1 flaw in the last diagram. Public key is used to encrypt and Private key is used to decrypt only as opposed to what is shown in the diagram with CA public/private key. Please let me know if I am wrong. Thanks
Ответить
I thought we were talking about Digital signatures not certificates.
Ответить


![[트로트] 디스코트로트7곡-박진석노래 [트로트] 디스코트로트7곡-박진석노래](https://invideo.cc/img/upload/bzZjRXV3cUNVZFg.jpg)