Asymmetric Encryption - Simply explained
Комментарии:

burda türk varmı
Ответить
omg thank you very much saved me bro ....I can understand much better now
Ответить
i am a noob and so i wonder, when emails use pgp or gpg as asymmetric encryption, why is sending data via email still unsecure in general?
Ответить
Great video! I couldn't wrap my brain around this concept and the video cleared things right up.
Ответить
Fails to explain how something can be encrypted with a key that can't be used for decryption.
Ответить
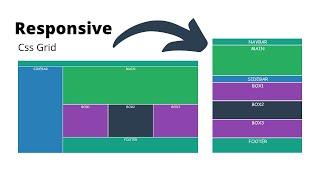
odin project
Ответить
This really helped me, Thanks!!!
Ответить
thanks
Ответить
Woah thank you so much
Helps a lot for someone who usually doesn't understand a thing 💀🙏🏻

Lets change it into "Public Locks and Private Keys"
Ответить
Short, sweet, and to the point. Thanks for this great info condensed in short amount of time.
Ответить
Thanks for the video!
Ответить
Beautifully put, thank you.
Ответить
great explained!
Ответить
Thank you very much
Ответить
So basically, you use somebody's public key to encrypt messages that only they can decrypt with their private key.
Ответить
great work thanks for good exmplain. finally i understand how is it working
Ответить
Am I the only one who doesn't get, how Alice's Encryption Program knows, what Bob's Private Key will look like?
Ответить
Excellent explanation - greatly appreciated!
Ответить
watched 2 times and uderstood succesfully
Ответить
Well explained......
Ответить
How Do you Unencrypted it with your private key? I'm weird, do you keep your key
Ответить
amazing video
Ответить
thank you very much for such a good explanation
Ответить
Fantastic explanation
Ответить
I think what you meant to say was that bitcoin uses cryptography for creating digital signatures, and digital fingerprint of blocks. The bitcoin network does not use encryption. Anyone can see the data written on the blockchain. Having said that, implementations of wallets tend to use encryption to secure keys. However, wallets are not directly a part of the bitcoin network!
Ответить
Thank you so much! This really answered all my remaining questions, just got taught it and asked things like, why would it be public when you can reverse the process and etc. That mailbox example really did it for me!
Ответить
Thanks for sharing
Ответить
Anyone here from The Odin Project? Keep it up, we can do it! :)
Also thanks for the video, the concept seemed almost alien to me but you've explained it in such a clear way that anybody could understand it

I am confused about something. If the attacker only steals Alice's private key, how can the attacker decrypt messages sent by Alice? If Alice sends a message to Bob, then only Bob's private key can decrypt the message. Correct? So why is the video claiming that the attacker able to decrypt messages that Alice sends to Bob, without having Bob's private key? Alice will need Bob's public key to encrypt the message she sends to Bob, and only Bob can decrypt it.
Ответить
crystal clear
Ответить
When they swap keys, could a hacker not intercept them and decrypt the message?
Ответить
fuck, Alice and Bob are at it again.
Ответить
sweet and simple , just what i needed , thanks a ton
Ответить
Awesome...
Ответить
thanks well explained
Ответить
Great 🤝
Ответить
Thanks Boss.
Ответить
Excellent explanation on asymmetric encryption. I was uncertain on how could the encryption of locking/unlocking the data worked since the private key never crossed the wire. You introduced and delivered that difficult concept in an easy relatable manner. Thank you for that! Best video ever. I now feel more confident about asymmetric encryption.
Ответить
simple and clear explanation ♥♥
Ответить
Assumption that Private key can not be derived using public key goes wrong in Post quantum world. That is where whole RSA security collapses.
Ответить
Finally, someone explains to me how it works. Thanks a lot!
Ответить
How does Alice knows how to encrypt the message that only Bob's private key can unlock? Surely Alice got to know Bob's private key somehow right?
Ответить
thank you !
Ответить








![это п#здец [заявка в ANTIKICKFLIP | ПРИНЯТА] это п#здец [заявка в ANTIKICKFLIP | ПРИНЯТА]](https://invideo.cc/img/upload/OG5tV2R2VTN0cDk.jpg)