Комментарии:

Perfect explanation😍
Ответить
Finally i reach out to this video after seeing many videos. Now everything is clear. Thanks
Ответить
Crystal clear explanation
Ответить
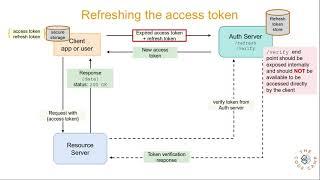
Question: if the refresh token is compromised without client or server knowing, can't the abuser constantly fetch new refresh tokens? It seems with this method you have to manually revoke access to a refresh token
Ответить
You are awesome 😎
Ответить
This is too much... Wtf is auth server?))) can't wr just use one server
Ответить
I wasted my time looking for clear information about this subject for hours.. and then I found your video, clear, concise and right to the point.. thank you.
I have a doubt though, are you sure the jwt token verification needs an auth server? ... I think the resource server can do that using a public key delivered by the auth server.

Concise and to the point.
Ответить
Awesome explanation Sir! Thank you very much.
Ответить
Very Good Explanation .Thank you .
Ответить
But how will administrator come to know that refresh token has been leaked?
Ответить
This is gem💎! Thanks alot!
Ответить